Learn how to configure and manage BIG-IP Local Traffic Manager (LTM) as it is commonly deployed in an application delivery network to achieve operational efficiency and maintain critical business applications. Through a combination of lecture and hands-on labs, explore features and functionality to process and modify traffic behavior using profiles, persistence, caching, compression, and source network address translation (SNAT).
Monitor application health at layers 3, 4, and 7, and implement dynamic load balancing methods. Use traffic management shell (TMSH), the Configuration utility, and Linux commands to create traffic processing and monitoring objects, observe the resulting traffic statistics, and effectively operate the BIG-IP LTM system. Customize application delivery with iRules, establish application security, and harden system security using BIG-IP LTM functionality.
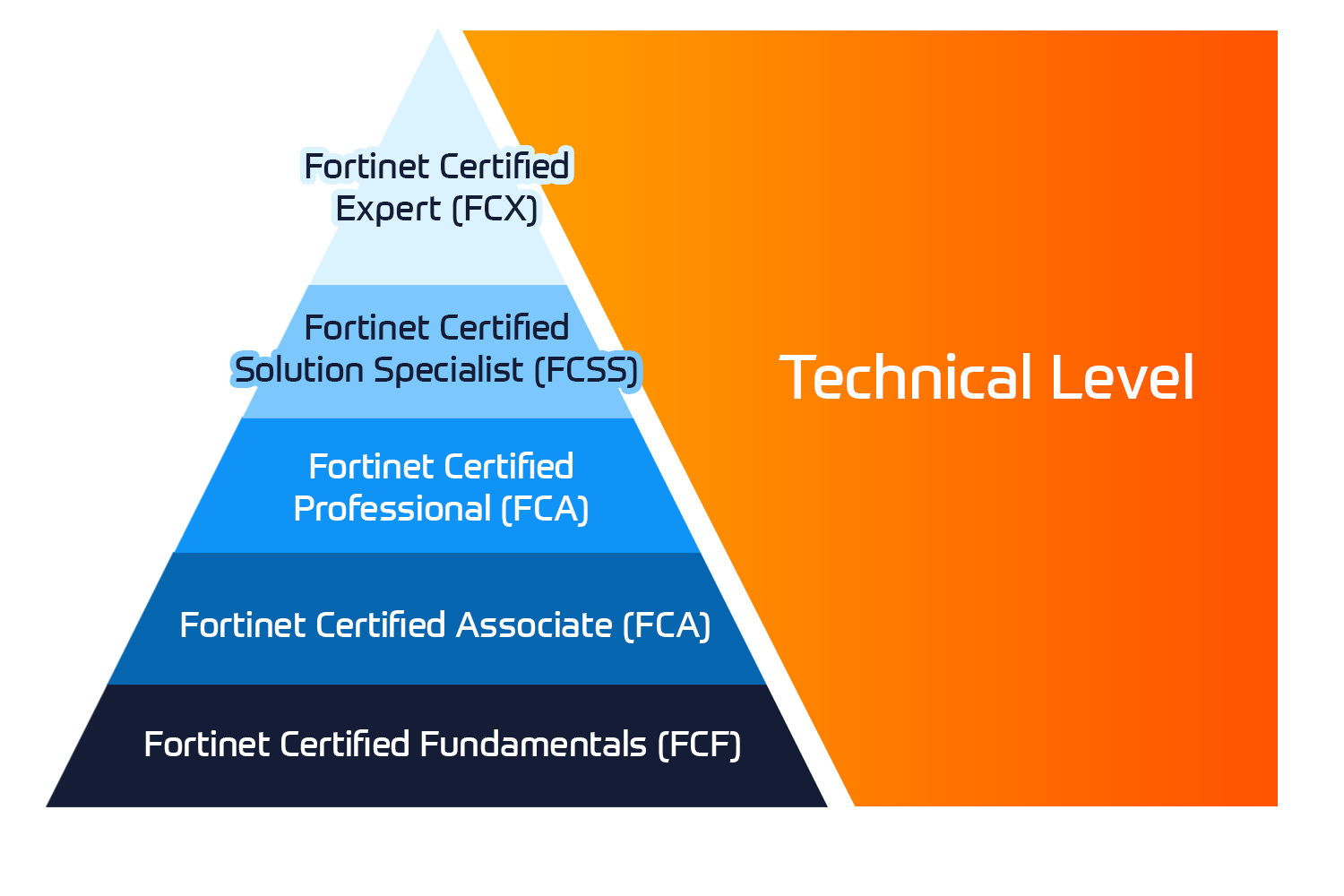
Associated certification:
- Technical Specialist Track
Exam/Test:
- EXAM 301A: BIG-IP LTM Specialist: Architect, Set up, Deploy

 United Kingdom
United Kingdom Germany
Germany Denmark
Denmark Sweden
Sweden Italy
Italy Netherlands
Netherlands Norway
Norway 















 Kesto
Kesto  Toimitus
Toimitus  Hinta
Hinta